Web Application and Network Penetration testing
None secure code leads to unintended use and massive consequences.
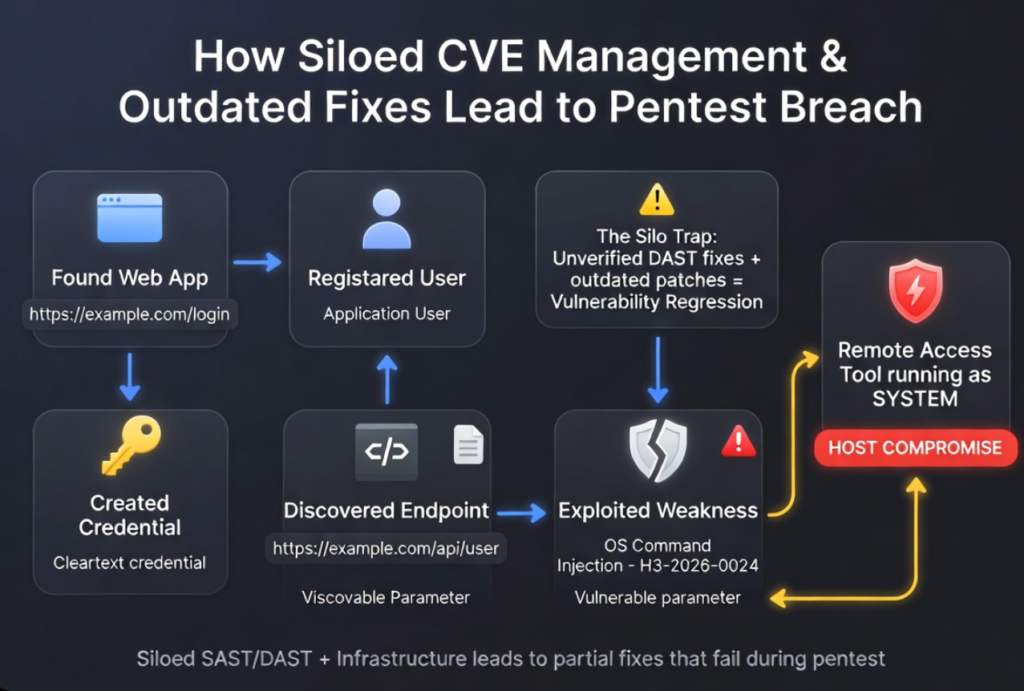
Dynamic Application Security Testing (DAST) simulates real hacker attacks on running applications (black-box testing). When findings are ignored, dismissed as “false positives,” or fixes are not properly verified post deployment, vulnerabilities come back or new ones slip in.
When companies choice not to address risks that are critical due to roles and responsibility those who proactively tracks and verifies known vulnerabilities or CVE’s, this removes follow through and regression testing discipline. As the result is the same bugs reappear, giving attackers an easy path in.
Dynamic Application Security Testing (DAST) simulates real hacker attacks on running applications (black-box testing). When findings are ignored, dismissed as “false positives,” or fixes are not properly verified post deployment, vulnerabilities come back or new ones slip in.
Network Penetration testing:
Firewalls and VPNs are your first line of defense and your most exposed targets. Outdated firmware doesn’t just fail to protect; it becomes the entry point for unauthenticated root access. Lundy Unlimited identifies the un-patched CVE’s in your edge appliances before attackers do.
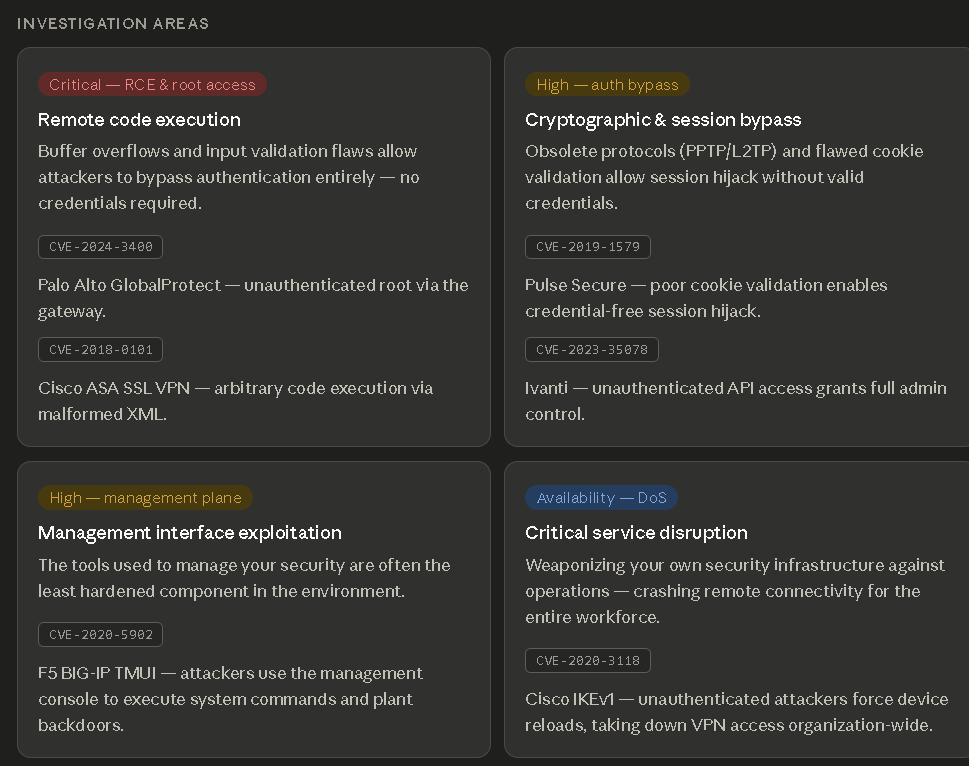
When companies choice not to address risks that are critical due to roles and responsibility those who proactively tracks and verifies known vulnerabilities or CVE’s, this removes follow through and regression testing discipline. As the result is the same bugs reappear, giving attackers an easy path in.