Breaking Active Directory: A Real Kerberos Attack Chain – From SPN to Shell
Phase 1: Initial Foothold The attacker starts with a low-privileged domain user account (e.g., via phishing, credential stuffing, or an initial compromise). No admin rights are needed just a valid domain credential as this is the assumed breach scenario. With a foothold, the attacker can now interact with the Kerberos Key Distribution Center (KDC) on the domain controller.
Phase 2: SPN Enumeration (Reconnaissance) Using the compromised domain user, the attacker queries Active Directory via LDAP to discover accounts with registered Service Principal Names (SPNs). SPNs uniquely identify services (like MSSQL, HTTP, or custom apps) and are typically tied to service accounts.
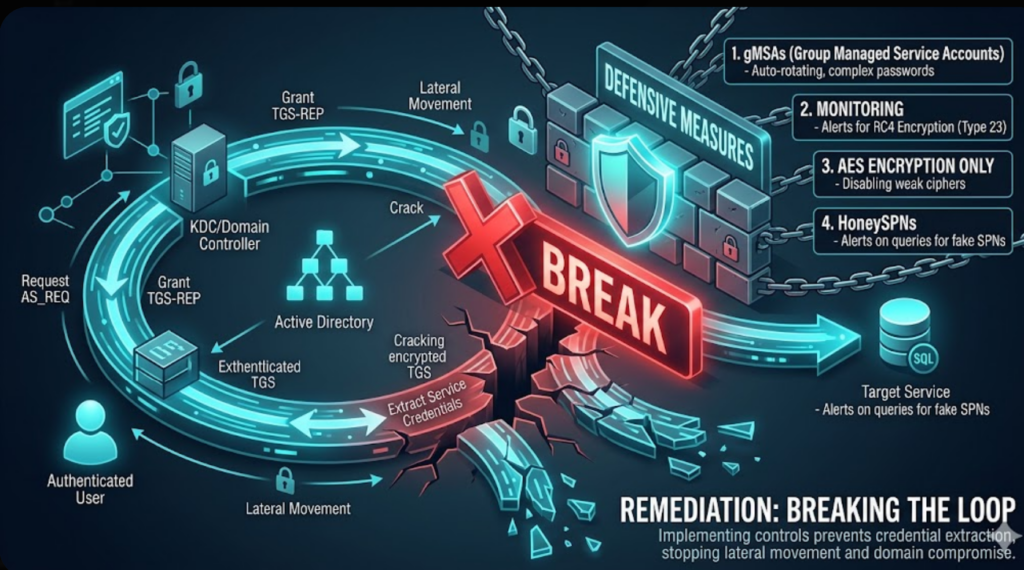
Kerberos attacks turn a single foothold into domain compromise and understanding TGTs, TGS tickets, and SPNs is the foundation. Mastering tools like Impacket and Hashcat turns theory into shells.